Imagine you’re trying to get past face-control at an exclusive club. You’ve put on a wig and dark glasses (that’s your VPN), but the bouncer at the door still shakes his head and sends you to the "ban list." Why? Because he isn't looking at your face. He noticed your unique sneakers, the scar on your hand, the way you hold your phone, and even the rhythm of your breathing.
In the world of affiliate marketing, this "set of traits" is called a Digital Fingerprint. In 2026, ad platforms have become so intelligent that attempting to access an account with just a VPN immediately triggers a high-risk flag. Let’s break down how this works and why.
The Illusion of Invisibility
Many beginners still believe that changing an IP address is 90% of the battle. In reality, in 2026, that is just the tip of a massive iceberg. If your IP says you are in London, but your system time is set to a different region—you’ve "burned" your cover.
Advertising giants like Facebook, Google, and TikTok collect hundreds of indirect markers to build your unique digital portrait. They don’t need to know your name; they just need your "hash"—a unique string of characters that distinguishes your computer from millions of others.
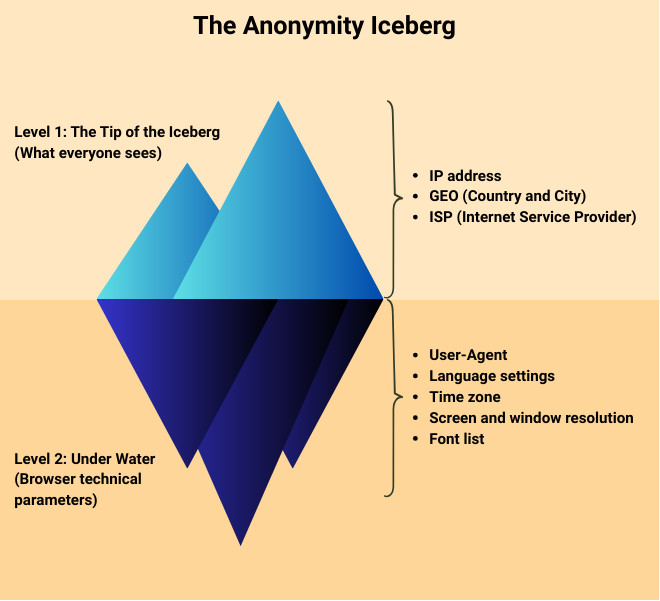
Cloaking.House works with the entire depth of the iceberg. We filter traffic based on a deep analysis of fingerprints that a standard VPN simply cannot hide.
Anatomy of a Fingerprint: What Your Browser Knows About You
Fingerprinting isn't magic; it’s the use of standard browser functions for tracking purposes. A website asks your browser to perform harmless tasks: render an invisible image, play a short sound, or list installed fonts.
Due to differences in video card drivers, Windows/macOS builds, and even physical "hardware" wear and tear, the result of these operations will be unique. For example, Canvas Fingerprinting technology analyzes exactly how your video card renders text and shadows. A difference of a single pixel—and your fingerprint becomes one of a kind.
Add to this AudioContext (analysis of the sound subsystem) and WebRTC (which can "leak" your real IP bypassing any proxy), and you’ll realize: hiding is useless. You must imitate.
Why Cloaking.House is Your Shield
Cloaking in the modern sense is not just a redirect. It is an intellectual filter that operates at the fingerprint analysis level. When someone clicks your link, Cloaking.House performs a "digital forensic audit" of the visitor within milliseconds.
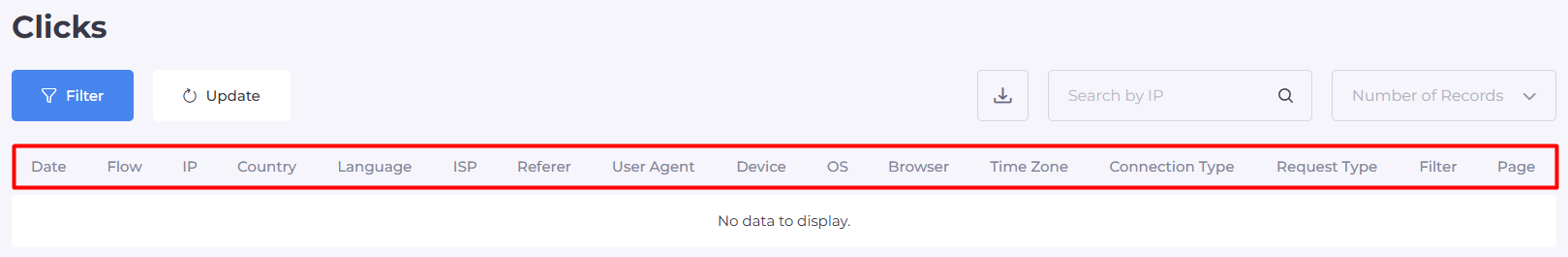
An ad network bot or a moderator always gives themselves away through their fingerprint. They often lack specific plugins, or their graphical parameters are too "sterile," which is typical for server-grade hardware. The system detects these anomalies and instantly sends such visitors to a "White Page" (Safe Page), while a real target user with a "live" fingerprint proceeds smoothly to the offer.
How Cloaking.House Analyzes Traffic:
| Parameter Group | What the System Checks | How It Protects Your Ads |
| Source Reputation | Analysis of the IP address against updated databases of data centers, Proxies, VPNs, and Tor exit nodes. | Automatically cuts off bots and automated check systems that always use server resources. |
| Technical Compliance | Checking the User-Agent for relevance and consistency with the declared operating system. | Identifies "suspicious" requests where software tries to mimic a mobile device while showing desktop traits. |
| Geographic Filter | Cross-referencing time zone, browser language, and regional settings with provider data. | Moderators often use tools that "glitch" on small details (e.g., a German IP with English system language). We see this. |
| Behavioral Markers | Analysis of the Referer (where the click came from) and interaction history with our filters. | We know the "handwriting" of major network moderators. If a fingerprint matches a check pattern, they will never see your offer. |
The main goal of Cloaking.House is to make protection absolutely invisible to the target client. The system runs on ultra-fast servers, so fingerprint analysis creates no delays during the transition.
While ad network bots are busy studying your perfect "white" page and finding no violations, real users with "clean" fingerprints are bringing you conversions. This is the technological advantage that allows an affiliate to sleep soundly.
The Trust Score Concept
In 2026, advertising platforms assign every visitor a Trust Score (reliability rating).
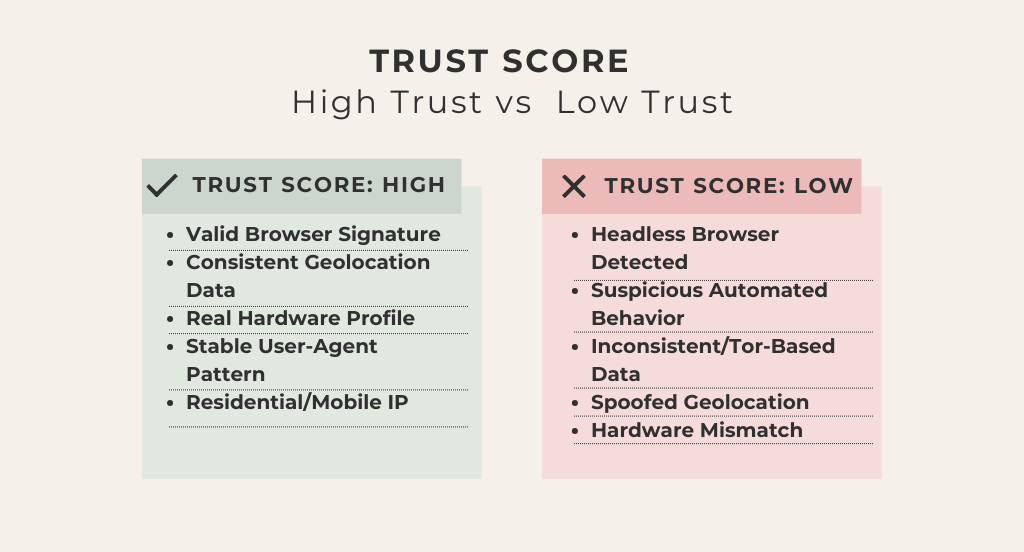
If your Fingerprint looks like that of an average person (typical screen resolution, standard fonts, logical GEO)—your Score is high. You get cheap reach and long account life.
If the system sees anomalies—your Score drops, and the account is sent for verification (Selfie, ID, Ban).
Cloaking.House acts as the perfect intermediary: it only allows those whose Trust Score matches a real buyer to reach your offer, while presenting a "white mirror" to those coming to inspect you.
How to Use This Knowledge for Profit
To ensure your campaigns live long and your ROI remains healthy, stick to the three rules of "digital hygiene":
Don’t skimp on proxies: Use high-quality mobile or residential proxies.
Use anti-detect browsers: They create that "bottom part of the iceberg"—masking parameters to make your profile unique yet natural.
Trust Cloaking.House with filtration: Even the best account will get banned if a moderator sees your real landing page. Our system analyzes thousands of fingerprint parameters.
Conclusion
In 2026, anonymity is not an absence of data, but an abundance of it. You must provide the ad network with a digital fingerprint so plausible that it leaves no room for doubt.
Cloaking.House handles the most difficult part of this job—recognizing those who are trying to check you. While the bots study your "white" page, you can calmly scale your campaigns and collect your profit.







Be the first to share your opinion!
We value your feedback — share your thoughts.